In today’s interconnected world, the security of software applications is of paramount importance. Software is the backbone of many businesses and critical infrastructure, and any vulnerability can lead to data breaches, financial losses, and damage to your reputation. To mitigate these risks, it’s crucial to implement robust security measures throughout the software development lifecycle. In this article, we’ll explore key security measures in software development that can help safeguard your digital assets.
key security measures in software development
1. Threat Modeling
Before writing a single line of code, it’s essential to identify potential security threats and vulnerabilities. Threat modeling is the process of systematically evaluating the application’s architecture and design to identify potential security weaknesses. This proactive approach allows developers to address security concerns early in the development process.
2. Secure Coding Practices
Writing secure code is fundamental to software security. Developers should be well-versed in secure coding practices, which include:
Input Validation: Sanitizing and validating user inputs to prevent injection attacks like SQL injection and Cross-Site Scripting (XSS).
Authentication and Authorization: Implementing strong authentication mechanisms and ensuring that users have appropriate authorization for accessing resources.
Error Handling: Avoiding the exposure of sensitive information in error messages and logs.
Secure Communication: Encrypting data in transit using protocols like HTTPS and TLS.
Session Management: Employing secure session management practices to prevent session fixation and session hijacking attacks.
3. Regular Security Testing
Security testing is an ongoing process that helps identify vulnerabilities and weaknesses in your software. It includes:
Penetration Testing: Ethical hackers simulate real-world attacks to identify vulnerabilities and weaknesses in the application.
Static Analysis: Automated tools analyze the source code to detect security flaws without executing the application.
Dynamic Analysis: Testing the application in a runtime environment to uncover vulnerabilities that may not be apparent in static analysis.
4. Patch Management
Keeping all components, libraries, and frameworks up to date is critical. Regularly apply security patches and updates to eliminate known vulnerabilities. Additionally, monitor security advisories and news for emerging threats that may require immediate attention.
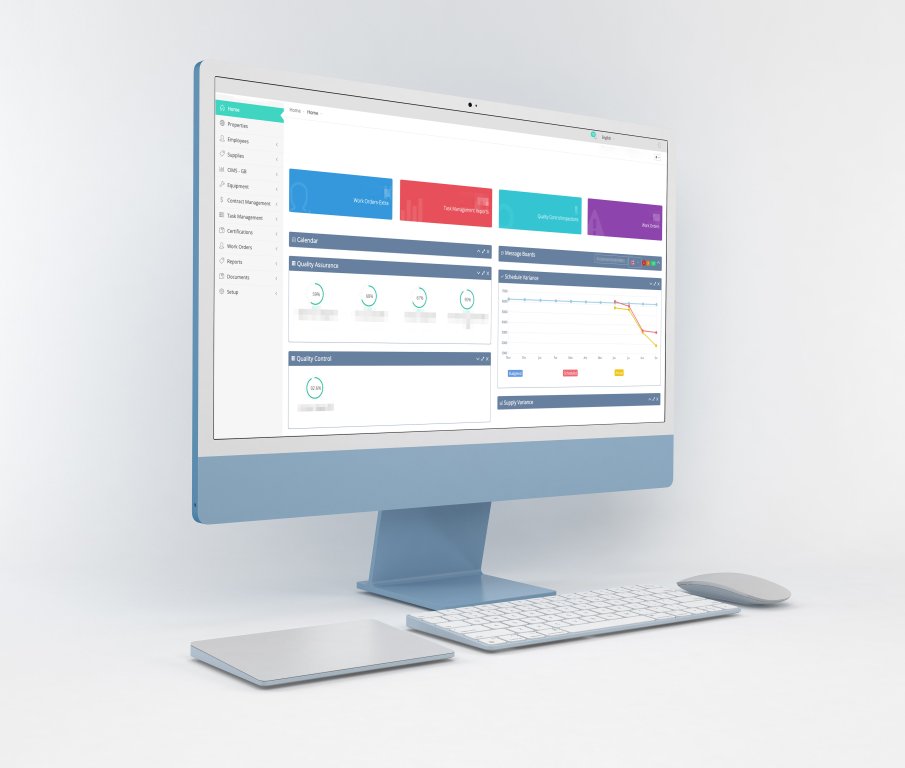
5. Secure Development Tools
Choose development tools and frameworks with built-in security features. Use security-focused libraries and frameworks that have undergone rigorous testing and are actively maintained.
6. Security Training and Awareness
Invest in ongoing security training for your development team. Ensure that they are aware of the latest security threats and best practices. Conduct regular code reviews with a focus on security.
7. Code Repository Security
Secure your code repositories by implementing access controls, requiring strong authentication for access, and regularly auditing repository activity.
8. Incident Response Plan
Prepare an incident response plan to effectively handle security incidents. Define roles and responsibilities, establish communication protocols, and have a clear plan for containment, investigation, and recovery.
9. Data Encryption and Privacy
Encrypt sensitive data both at rest and in transit. Comply with data protection regulations like GDPR, HIPAA, or CCPA, depending on your business and user data.
10. Regular Security Audits
Conduct periodic security audits to assess the overall security posture of your application. These audits can identify weaknesses that may have been overlooked during development.

Cybersecurity ecosystem
The Data Security Council of India has forecast that the cybersecurity ecosystem will expand up to a point where nearly one million professionals will be required by 2025. Additionally, the demand for cloud security skills is estimated to grow by 115% between 2020 and 2025, representing almost 20,000 job openings, Narayan added.
An extensive exercise in reskilling and/or upskilling the existing workforce, believe staffing experts, is one of the ways that telcos can future proof their work.
Indian mobile phone operators are expected to at least double their investments on network security with the 5G roll out expected to spark a surge in network vulnerabilities, which assume critical importance especially for enterprises.
However, it is already proving to be a challenge for telcos to have robust security teams.
“Even if we do not talk about 5G (specifically), the security talent in general in the country is very sparse at the moment. We need to get more (security) professionals in the system”
Security measures in software development are not a one-time effort but an ongoing commitment to protecting your digital assets and your users’ data. By implementing these security practices throughout the software development lifecycle, you can significantly reduce the risk of security breaches and ensure that your software applications remain robust and trustworthy in the face of evolving cyber threats. Remember that proactive security measures are an investment in your business’s reputation and long-term success.



We didn’t invent the term “fools with tools.” Still, it’s a perfect definition for the practice of buying a stack of sophisticated cybersecurity technology that’s impossible to manage without an MSP or the budget of a Fortune 500 IT department.